Looney Tunables: Local Privilege Escalation in the glibcs ld.so CVE-2023-4911 Proof of Concept
It was discovered that the GNU C Library incorrectly handled the GLIBC_TUNABLES environment variable.
An attacker could possibly use this issue to perform a privilege escalation attack.
A buffer overflow was discovered in the GNU C Librarys dynamic loader ld.so while processing the GLIBC_TUNABLES environment variable.
This issue could allow a local attacker to use maliciously crafted GLIBC_TUNABLES environment variables when launching binaries with SUID permission to execute code with elevated privileges.
More info at:
Fix:
The problem can be corrected by updating your system to the following package versions example below:
Ubuntu 23.04: libc6 - 2.37-0ubuntu2.1
Ubuntu 22.04: libc6 - 2.35-0ubuntu3.4
For PoC of CVE-2023-4911 Looney Tunables
Full credits to leesh3288 for the PoC used in this demo
Twitter: 0x10n
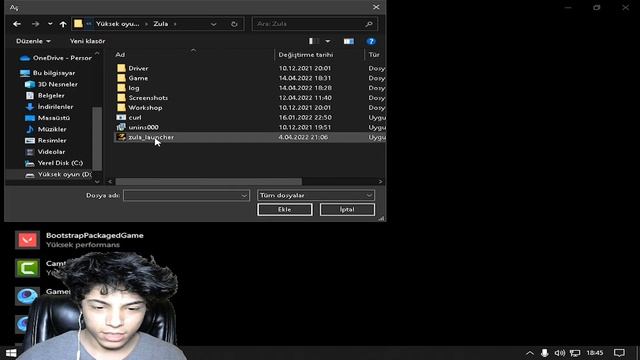
P.S: This one worked for me:
Tested on:
Ubuntu 22.04.3 LTS
glibc version: GLIBC 2.35-0ubuntu3.1
Forked version of PoC:
Источник: rutube.ru

 Канал на RUTUBE:
Канал на RUTUBE: