Certificate Bypass: Hiding and Executing Malware
Tom Nipravsky- BlackHat 2016 Presentation
Malware developers are constantly looking for new ways to evade the detection and prevention capabilities of security solutions.
In recent years we have seen many different tools such as packers and new encryption techniques help malware reach this goal of hiding the malicious code.
If the security solution cannot unpack the compressed or encrypted malicious content or at least unpack it dynamically then the security solution will not be able to identify that it is facing malware.
To further complicate the matter we present a new technique for hiding malware encrypted and unencrypted inside a digitally signed file while still keeping the file with a valid certificate and executing it from the memory using a benign executable which acts as a reflective EXE loader written from scratch.
Our research demonstrates our Certificate Bypass tool and the Reflective EXE Loader.
During the presentation we will focus on the research we conducted on the PE file structure.
We will take a closer look at the certificate table and how we can inject data to the table without damaging the certificate itself the file will still look and be treated as a valid digitally signed file.
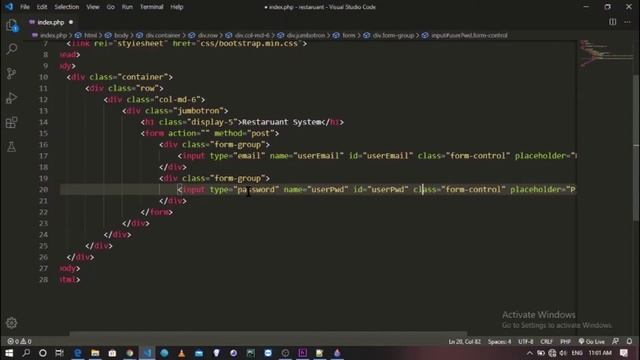
We will examine the tool we wrote to execute PE files from memory without writing them to the disk.
We will cover the relevant fields in the PE structure as well as the steps required to run a PE file directly from the memory without requiring any files on disk.
Last we will conclude the demonstration with a live example and show how we bypass security solutions based on the way they look at the certificate table.
Источник: rutube.ru

 Канал на RUTUBE:
Канал на RUTUBE: 




![[AOR-GT3] 4th Race at Laguna Seca - No Aston territory!? (PC/Project CARS)](https://pic.rtbcdn.ru/video/e6/cf/e6cf3c27bd1ab4e8bbd742f81f4e33a7.jpg)
![Touch English Song - If you are wearing red [get.gt].mp4](https://pic.rtbcdn.ru/video/2026-04-25/fe/31/fe316414b24f9ace207dd477f3298457.jpg)